










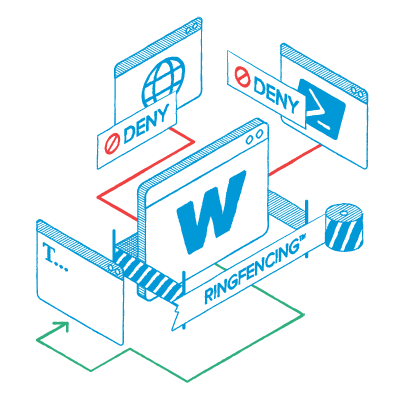
Allow what you need. Block everything else by default, including ransomware and rogue code.






















Get ironclad Zero Trust cybersecurity with granular control over every app, script, and process in your environment. Welcome to a world with fewer alerts, less blind spots, and a new level of control—all backed by unmatched 24/7 support.
Deny-by-default is your fastest way to break ransomware.
See how it works

Endpoints are validated continuously, evidence is logged automatically, gaps are flagged, and fixes can be deployed.
See how it works

If an attacker logs in from an unrecognized laptop next door or even on the same network, they’re stopped instantly.
See how it works

Remove forgotten standing privilege and cut risks immediately.
See how it works
Make data exfiltration structurally difficult.
See how it works
Stop a compromised machine from becoming an enterprise-wide incident.
See how it works







Try ThreatLocker free for 30 days and experience full Zero Trust protection in your own environment.
Schedule a customized demo and explore how ThreatLocker aligns with your security goals.
Just starting to explore our platform? Find out what ThreatLocker is, how it works, and how it’s different.