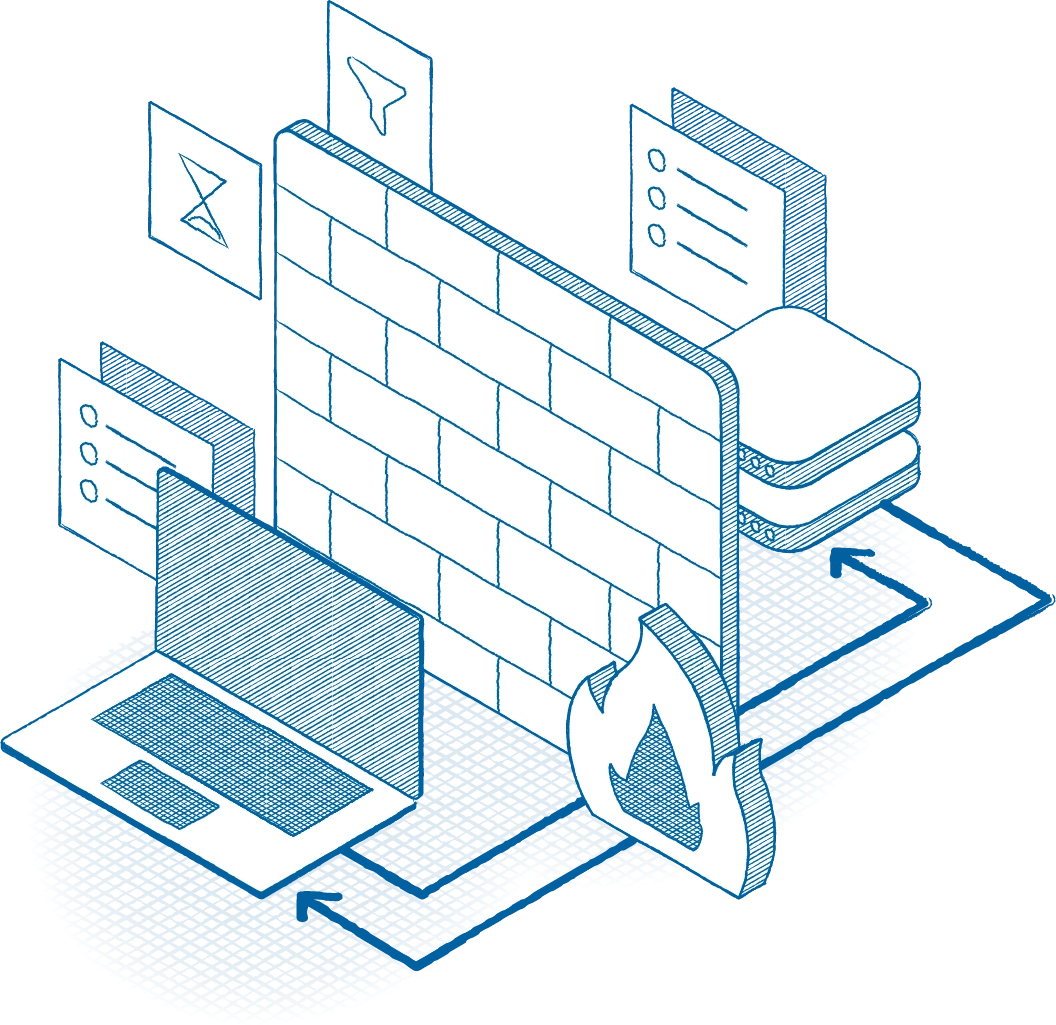
ThreatLocker endpoint firewall is a host-based firewall for endpoints and servers that gives you complete control over network traffic by enforcing access based on device, IP, port, and policy.
The benefit: You eliminate unauthorized connections while maintaining flexible, scalable control across your entire environment.


