Most data exfiltration begins with something executing. If untrusted software can execute, it can stage data, compress it, encrypt it, or quietly transmit it out of your environment. The fastest way to stop exfiltration is to stop unknown execution in the first place.
So often attackers abuse the applications you already trust. When legitimate tools are allowed to do more than they should, they become the attacker’s launchpad. Application containment changes that. It defines clear behavioral boundaries so trusted software can perform its job. This way, you can keep every application in its lane and break the attack chain before it begins.
The more users, applications, or devices can touch your sensitive data, the easier theft becomes in your organization. Granular, policy-driven access control ensures only the right people using the right applications can access the right data, at the right time.
Removable media remains one of the simplest, fastest ways to bypass perimeter controls and export sensitive files. Without strict policy enforcement, one unknown device can move gigabytes in minutes. Locking down removable media closes that silent exit path before it becomes a breach.
Passwords are stolen every day, and tokens are intercepted. And sometimes MFA prompts are approved when they shouldn’t be. Don’t rely on a single layer to hold back a determined attacker. Zero Trust cloud access adds a second, decisive control: the device. Access now will be granted only when the device is trusted and the connection follows an approved path.
Once inside, attackers move quietly from system to system, searching for file servers, backups, and high-value data. In fact, most large breaches expand through lateral movement. With strong network control, you can stop this spread. When every device-to-device connection must be explicitly approved, the network stops being an open highway and becomes a series of guarded checkpoints. Sensitive servers cannot be casually reached and data cannot be quietly siphoned from across the environment.
What if your EDR acted instantly to help prevent data exfiltration. With ThreatLocker real-time threat detection capabilities, we will help you automatically identify abnormal behavior and enforce predefined policies immediately. The moment suspicious activity appears, devices can be isolated, risky processes shut down, and attacker pathways closed, without waiting on human review or cloud delays. Your detection strategy becomes immediate containment.
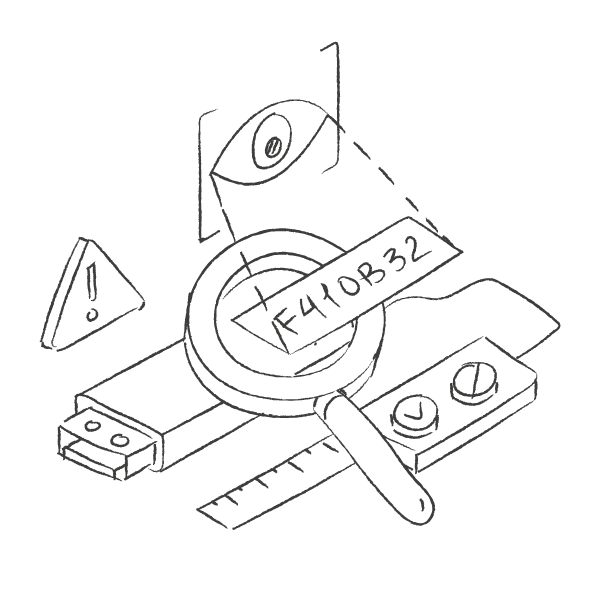
Most breaches begin with simple misconfigurations: a forgotten admin account, an overly permissive firewall rule, an unmonitored USB port. Small gaps can create big risk. With ThreatLocker, you gain continuous visibility into those gaps and clear, actionable steps to close them before attackers or auditors find them.
