Linux zero-day could allow underprivileged local users to obtain root access
Privilege escalation is dangerous for any organization. If an attacker gains elevated access to your environment, they can manipulate almost anything on your system and potentially compromise neighboring devices.
A new high-severity vulnerability in Linux is enabling just that.
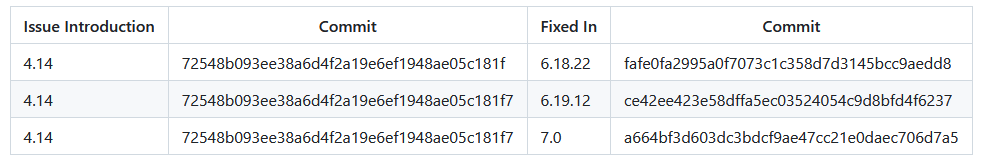
CVE-2026-31431, known as Copy Fail, is a local privilege escalation (LPE) flaw within the Linux kernel, enabling unprivileged local users with the ability to perform privilege escalation on virtually all major Linux distributions since 2017.
This is made possible due to a logical flaw in the Linux kernel’s AF_ALG AEAD (authenticated encryption with associated data) handling, where page-cache-backed file pages can be chained into a writable scatterlist during an in-place decryption operation.
In this article, the ThreatLocker Threat Intelligence team analyzes the flaw and provides mitigation strategies.
Copy Fail CVE-2026-31431 analysis
The authencesn algorithm then performs a 4-byte scratch write beyond the intended output boundary, corrupting the in-memory page cache of a readable file without modifying the file on disk. Because setuid binaries are loaded from the page cache, an unprivileged local user can abuse this corruption path to gain root privilege. This vulnerability can be abused through a 732-byte Python script or equivalent Go/Rust implementation to obtain root on nearly all Linux distributions available since 2017.
Page caches are used by the Linux kernel to make accessing objects more efficient. This is done by storing a copy of the object in memory, so that subsequent attempts to access it can be read directly from that memory space.
Several kernel capabilities are chained together to perform this exploit, but the core issue comes from page caches in memory being written to outside of expected protections by the kernel. Write actions made to page caches are normally regulated by the kernel and handled properly.
The Copy Fail exploit bypasses these restrictions entirely, allowing 4 bytes of any page cache in memory to be overwritten. Although 4 bytes may seem insignificant, changing the right value or instruction can make drastic differences.
Demonstration
Copy Fail demonstration
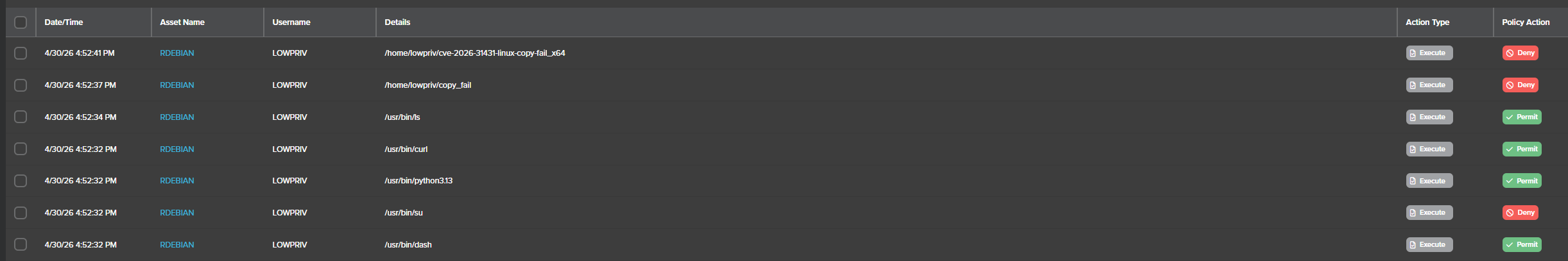
ThreatLocker stopping Copy Fail
Who is affected by Copy Fail?
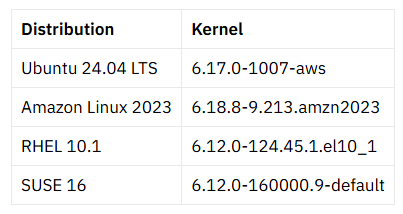
Most major Linux distributions that have not incorporated upstream patches remain susceptible.
What can you do to mitigate CVE-2026-31431?
Applying proper patches should be prioritized to fully mitigate and remove the vulnerable code that introduces the vulnerability.
If patching in a timely manner is not feasible, disabling the algif_aead module will mitigate the attack surface. Should the algif_aead module be already loaded into memory, running rmmod will unload it from the kernel.
echo "install algif_aead /bin/false" > /etc/modprobe.d/disable-algif.conf
rmmod algif_aead 2>/dev/null || true Strategies to prevent zero-day attacks
Zero-day vulnerabilities such as Copy Fail are ones that are unknown to the vendor. So when attackers decide to exploit a zero-day, detection solutions that are only looking for known vulnerabilities or known malicious code are already on the back foot.
Zero-day attacks require Zero Trust controls.
With a Zero Trust framework, you are denying anything that is not previously approved and continuously verifying every request. This means unknown scripts, malicious or not, are not allowed to execute.
Least privilege access is also enabled, preventing unprivileged users from accessing files or applications they do not have permission for.
How ThreatLocker prevents zero-days
ThreatLocker Application Allowlisting mitigates vulnerabilities such as CopyFail, blocking exploit code from executing by default.
In this instance, it can be leveraged to restrict access to python or the su binary, preventing the python script exploit from executing. Compiled versions of the Go or Rust exploit port will be blocked by the Allowlisting default-deny policy.
In addition, ThreatLocker Privileged Access Management removes broad administrative access and prevents privilege abuse before it turns into lateral movement or ransomware.
Zero Trust is the answer to zero-days
Zero-day vulnerabilities expose the fundamental weakness of traditional, detection-based security controls. If the vulnerability is unknown, reactive defenses fall short.
Zero Trust instead assumes everything is a threat and denies by default instead of relying on signatures or prior knowledge of an attack.
New vulnerabilities and more sophisticated attacks are inevitable, and faster detection isn’t the answer. Instead, remove the opportunity for exploitation all together.
Experience Zero Trust in your environment with a customized demo from ThreatLocker.