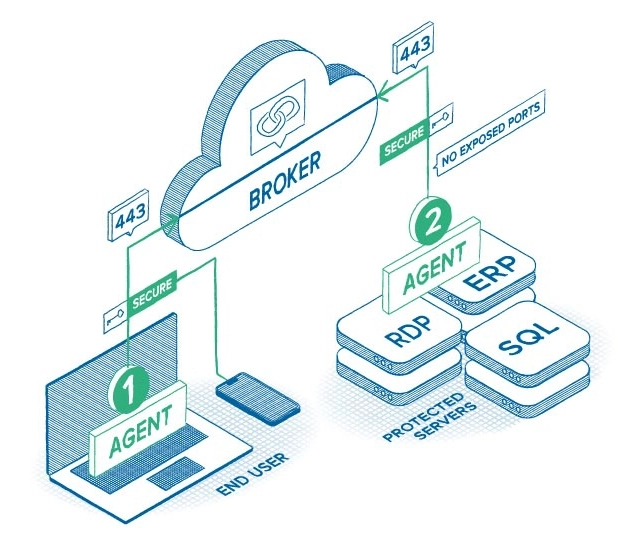
Zero Trust Network Access (ZTNA) with ThreatLocker is a modern approach to securing connectivity that ensures only authorized users on approved devices can access specific internal resources, without exposing your network to the internet.
The benefit: You dramatically reduce your attack surface while simplifying secure access for users.


