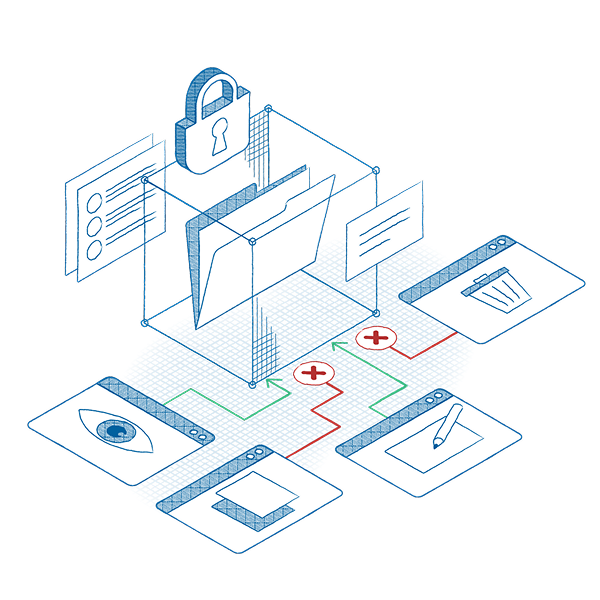
Pair data access policies with application containment.
Limit which applications can access sensitive folders, and then restrict what those applications can do.
For example:
Allow Excel to open finance files. Prevent it from launching PowerShell or making outbound connections. Now even if a trusted app is hijacked, it can’t exfiltrate data.
Request info