Newly discovered vulnerability looks like Copy Fail 2.0
CVE-2026-43284, commonly known as "Dirty Frag," is a critical local privilege escalation vulnerability located in the Linux kernel's IPsec ESP (esp4 and esp6) subsystems. Similar to the "Dirty Pipe" and "Copy Fail" vulnerabilities, it allows an unprivileged local attacker to exploit unsafe in-place cryptographic processing to write to file-backed page-cache pages.
Leveraging this flaw facilitates the corruption of privileged files, allowing an attacker to easily execute arbitrary code and gain full root access on affected Linux distributions.
At the time of writing, there is no known patch for the affected versions of Linux, and CVE-2026-43500 has been reserved for tracking purposes. In this article, the ThreatLocker Threat Intelligence team analyzes the vulnerability and addresses mitigation strategies and affected Linux versions.
How Dirty Frag works: 2 vulnerabilities linked to gain root privileges
Xfrm -ESP Page-Cache Write
The “xfrm-ESP Page-Cache Write” technique targets the Linux XFRM/IPsec ESP receive path and exploits improper handling of fragmented socket buffers (sk_buff) that reference page-cache-backed memory.
The attack begins by creating a pipe-backed page-cache reference using splice(), similar in concept to Dirty Pipe-style page pinning. The attacker then constructs a specially crafted non-linear shared socket buffer (SKB) whose fragments point into the cached page associated with the target binary, /usr/bin/su.
When the packet reaches the ESP decapsulation logic in esp_input(), the kernel attempts to decrypt and rewrite packet data in place. Because the SKB is assumed to be writable, and the required copy-on-write enforcement (skb_cow_data()) is skipped in this path, the crypto layer writes directly into the referenced page rather than into private packet memory. This converts what should be transient network-buffer mutation into persistent corruption of cached file contents.
RxRPC Page-Cache Write
The RxRPC Page-Cache Write vulnerability, known as CVE-2026-43500, is the second half of the broader "Dirty Frag" exploit chain.
Introduced into the Linux kernel in June 2023, this flaw performs an eight-byte in-place decryption directly on a splice-pinned page cache page without requiring user-namespace privileges.
The vulnerability exploits the zero-copy send path where splice() plants a reference to a read-only page cache page location (such as /etc/passwd or /usr/bin/su) into the "frag" slot of a sender-side shared socket buffer (SKB).
After this, the receiver-side kernel code performs in-place cryptographic operations directly on the planted frag, permanently modifying the page cache in RAM. By abusing zero-copy mechanisms such as splice() threat actors can leverage arbitrary writes to silently corrupt read-only systems directly in memory.
How Dirty Frag compares to Copy Fail
Although the CopyFail vulnerability is similar in using corrupted page caches to escalate privileges, this exploit uses a dual vulnerability approach as opposed to the single path that CopyFail takes.
As addressed in a recent post, CopyFail takes advantage of file-backed page caches being placed into writable scatterlists, allowing them to be written to by an in-place decryption algorithm.
DirtyFrag combines two separate procedures, xfrm-ESP and RxRPC, which both allow a write action to the page cache of sensitive binaries. Where some environments may restrict the creation of the user namespaces needed by xfrm-ESP, they may have the rxrpc.ko module built, which is used by RxRPC for the same effect.
Neither CVE-2026-43500 (RxRPC) nor CVE-2026-43284 (xfrm-ESP) alone provide sufficient reliability for full root escalation, but when combined, the chained exploits achieve immediate root on most distributions. This allows DirtyFrag to cover a much wider subset of inherently vulnerable victims than CopyFail.
Linux versions affected by Dirty Frag
The Dirty Frag exploit was validated against multiple modern Linux distributions and kernel versions. This list is incomplete, and considering the severity of this exploit, any Linux distributions of concern should be individually tested for vulnerability.

How to mitigate Dirty Frag vulnerability
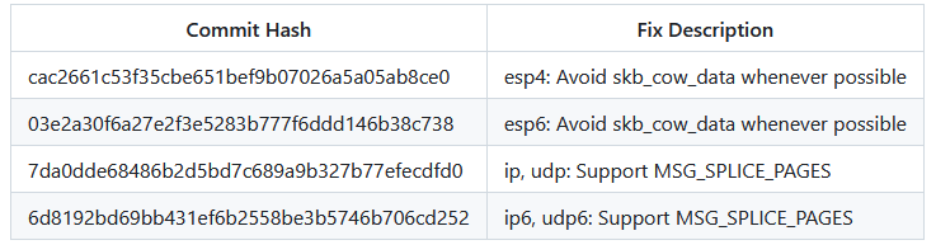
The following changes have been made to address CVE-2026-43284, but these do not cover the gaps introduced by CVE-2026-43500.
The following command was also included in the public disclosure. It removes the modules that contain the vulnerability and clears the page cache.
sh -c "printf 'install esp4 /bin/false\ninstall esp6
/bin/false\ninstall rxrpc /bin/false\n' >
/etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null;
echo 3 > /proc/sys/vm/drop_caches; true"

.jpg)