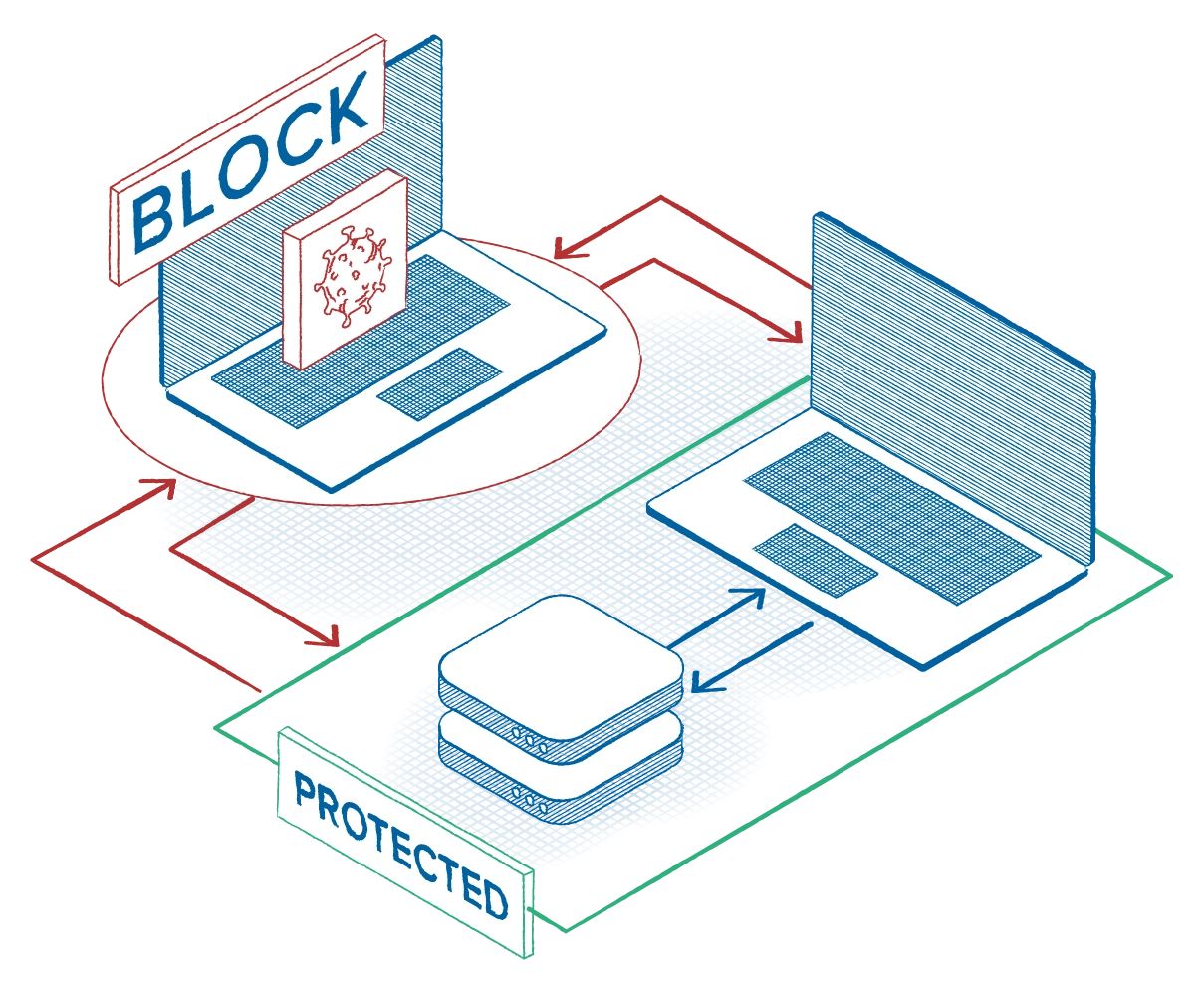
Build a strong, layered deny-by-default policy stack. Start with execution control, deny unknowns by default, approve only what your business needs; create containment rules for office, browsers, PowerShell; next—close lateral paths (east-west traffic, allow server access to approved devices only). Finally, automate the response: Trigger device isolation, restrict file access, and shut down risky processes the moment abnormal behavior appears.
Request info