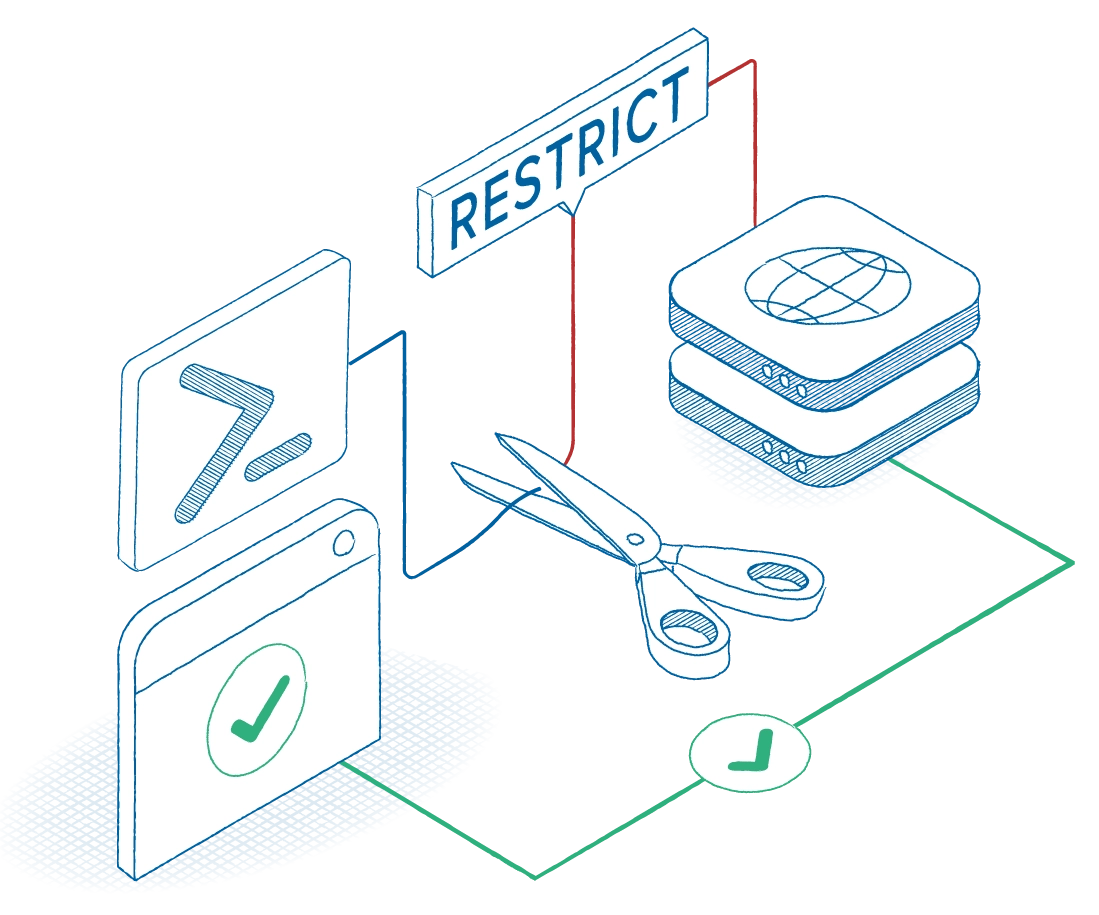
Make data exfiltration structurally difficult.
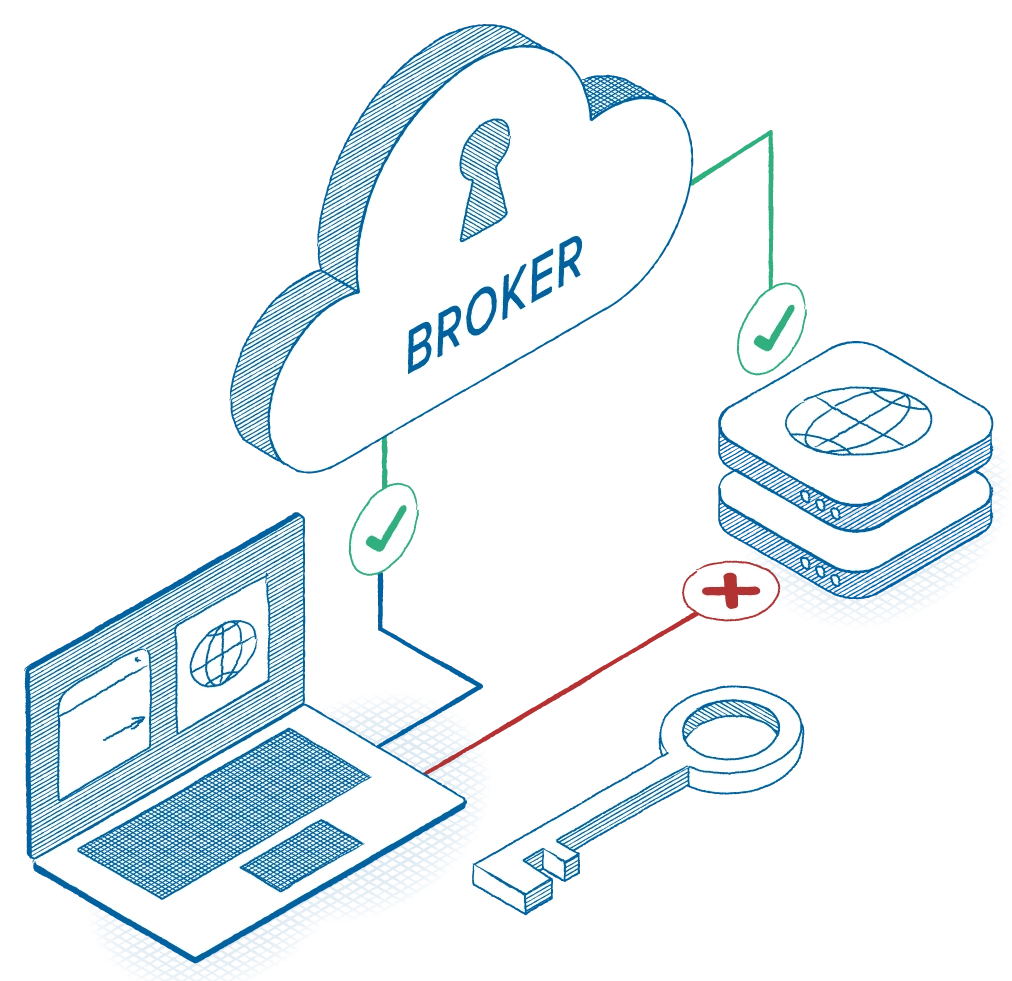
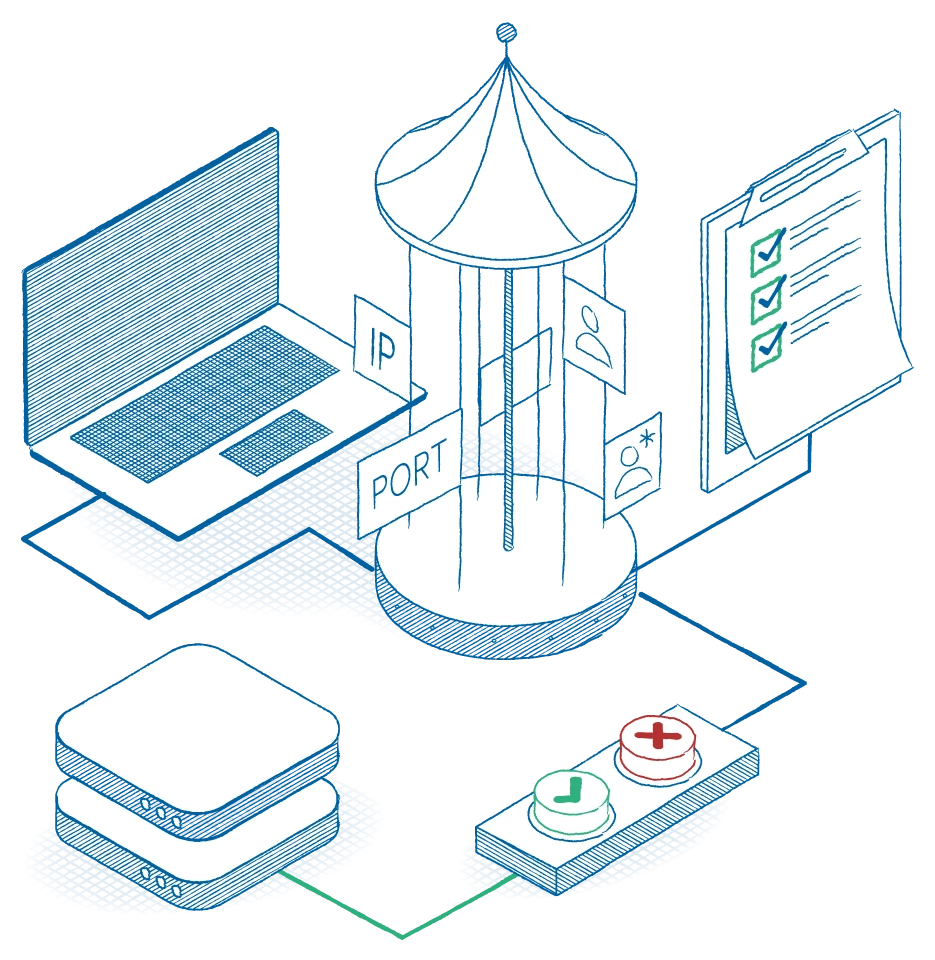
Enforce execution control, device validation, and policy-driven data access across your entire environment to block untrusted software, contain trusted tools, restrict data pathways, and validate every device. When access is policy-bound and denied by default, data theft becomes dramatically harder to execute.