Deploy the unified Zero Trust Platform trusted by enterprise security leaders worldwide to protect your users, devices, and networks and stop attacks before they spread.
Enables you to allow what you need, and block everything else, including ransomware
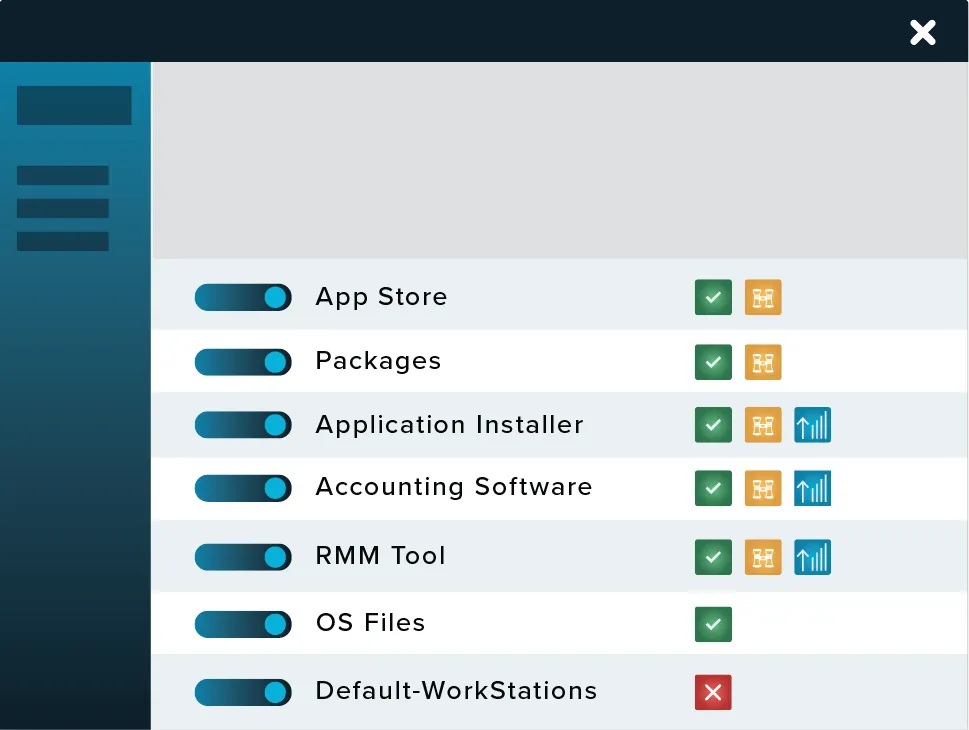
Allowlisting has long been considered the gold standard in protecting businesses from known and unknown executables. Unlike antivirus, Allowlisting puts you in control over what software, scripts, executables, and libraries can run on your endpoints and servers.
This approach not only stops malicious software, but it also stops other unpermitted applications from running. This approach greatly minimizes cyber threats by stopping rogue applications from running on your network.


Giving you complete control to help you manage your applications and better protect your endpoints.
Controlling what software can run should be the first line of defense when it comes to better protecting yourself against malicious software. Ringfencing adds a second line of defense for applications that are permitted. First, by defining how applications can interact with each other, and secondly, by controlling what resources applications can access, such as networks, files, and registries. Ringfencing is an invaluable tool in the fight against fileless malware and software exploits.

Cloud-managed endpoint and server firewall with dynamic ACLs to lockdown your endpoints and block unwanted network traffic.
Network Control allows for total control of inbound traffic to your protected devices. Using custom-built policies, you can allow granular access based on IP address or even specific keywords. Unlike a VPN that needs to connect through a central point, ThreatLocker Network Control is a simple connection between server and client. ThreatLocker Network Control is built in a way that creates a seamless experience, enabling users to work as normal while eliminating the need for a solution, such as a VPN.
Network Control gives users the ability to configure network access to endpoints using global and granular policies.
The cloud-managed solution provides customers with a centralized view of endpoint policies across your customers.
Network Control enables users to deny all traffic to published servers while only allowing a single IP address dynamically or even a keyword. This is great for users who travel often.

Run select applications as a local admin and remove local admin permissions without stopping productivity.
When it comes to adding extra layers of security to your cybersecurity stack, it's important to always add a human layer. Users with admin access are often the weakest link across your network, so their movements must be monitored and tracked.
ThreatLocker Elevation Control provides an additional layer of security by giving IT administrators the power to remove local admin privileges from their users, whilst allowing them to run individual applications as an administrator.
Gives you the ability to approve or deny an individual’s administrator access to specific applications within an organization even if the user is not a local administrator
Users can request permission to elevate applications and add notes to support their requests
Enables you to set durations for how long users are allowed access to specific applications by granting either temporary or permanent access
In combination with ThreatLocker Ringfencing, ensures that once applications are elevated, users cannot jump to infiltrate connected applications within the network
Giving you complete control over your storage devices, including USBs and network shares.
ThreatLocker® Storage Control is an advanced storage control solution that protects information. We give you the tools to control the flow and access of data. You can choose what data can be accessed, or copied, and the applications, users, and computers that can access said data. By using ThreatLocker®, you are in control of your file servers, USB drives, and your data. Most data protection programs on the market are butcher knife solutions to a problem that requires a scalpel. Blocking USB drives and encrypting data-storage servers can help secure your organization’s private data, but these tools don’t take into account that this data still needs to be quickly accessible. Waiting for approval or trying to find a device that’s allowed to access the needed files can drain hours of productivity.
Detect and identify suspicious activity within your environment.
ThreatLocker Detect looks for any anomalies that may make an environment vulnerable to a cyberattack. It analyzes data from ThreatLocker modules and notifies the admin if their system is using a version of software that's known to have cyber vulnerabilities. Should a breach be attempted, ThreatLocker Detect can take steps to defend the system, such as taking automatic remediations, and Application Control will block any malicious payloads.
Using industry-known indicators of compromise, ThreatLocker Detect can detect and alert IT professionals that their organization may be under an attempted attack based on customizable thresholds and notification methods.
Set policies to enable, disable, or create Application Control, Storage Control, or Network Control policies in response to specified observations.
Policies can be tailored to alert and respond differently based on the threat level to reduce alert fatigue.
IT admins can easily share their own ThreatLocker Detect policies or “shop” for vetted policies shared by their industry peers and the ThreatLocker team.

Unlike antivirus or traditional EDR, ThreatLocker Allowlisting solution puts you in control of what software, scripts, executables, and libraries can run on your endpoints and servers. This approach stops not only malicious software in its tracks but also stops other unpermitted applications from running. This process greatly minimizes cyber threats and other rogue applications from running on your network.
Normally, applications have access to all the same data as the end user. If an application is absolutely necessary, ThreatLocker Ringfencing can implement Zero Trust controls comparable to, but more granular than, traditional application containment tools. ThreatLocker Ringfencing controls what applications are able to do once they are running. By limiting how software can interact on your devices, ThreatLocker can reduce the likelihood of an exploit being successful or an attacker weaponizing legitimate tools such as PowerShell. These controls can prevent applications from interacting with another application, your files, data, or the internet.
Elevation Control puts IT administrators in the driver’s seat, enabling them to control specific applications that can run as a local admin without giving users local admin rights. With applications such as QuickBooks that need to run with local admin access, elevation control can limit that access without impacting operational workflow, which can prevent the further spread of an attack, like application hopping, in case there is a breach in the endpoint.
ThreatLocker Storage Control provides policy-driven control over storage devices, whether the storage device is a local folder, a network share, or external storage such as a USB drive. Storage Control allows you to set granular policies, such as blocking USB drives or blocking access to your backup share except when your backup application is accessed.
Try ThreatLocker free for 30 days and experience full Zero Trust protection in your own environment.
Schedule a customized demo and explore how ThreatLocker aligns with your security goals.
Just starting to explore our platform? Find out what ThreatLocker is, how it works, and how it’s different.